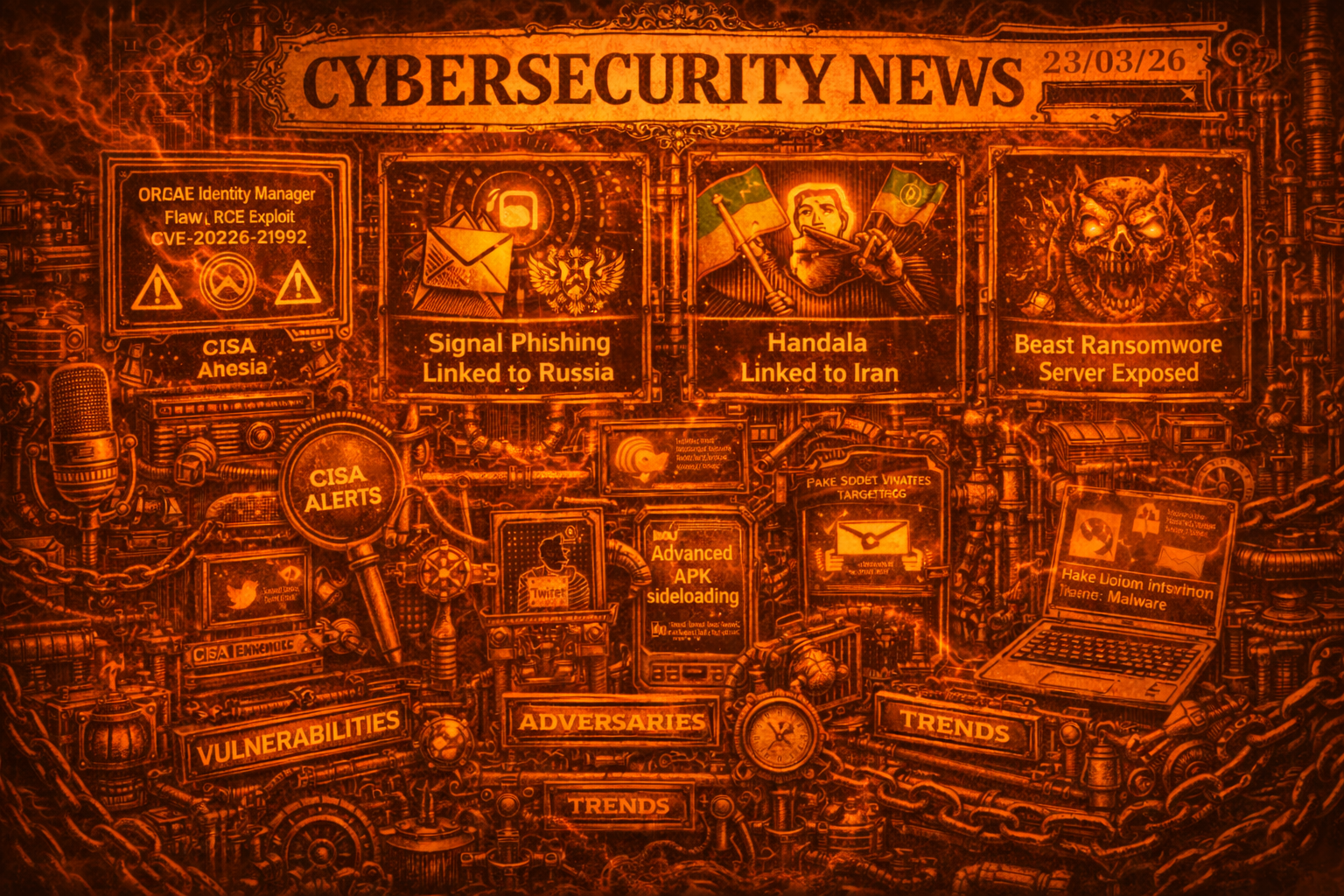
Cybersecurity Newsfeed - 23/03/26
Daily cybersecurity news covering vulnerabilities, adversaries, trends, breaches, and other notable security developments.
Cybersecurity Newsfeed
📅 23/03/26
🛡️ Vulnerabilities
Oracle Identity Manager RCE (CVE-2026-21992): Oracle issued an out-of-band security update for a critical remote code execution vulnerability. Unauthenticated attackers can execute arbitrary code with elevated privileges, potentially leading to full system compromise. Organizations are urged to patch immediately. More info
CISA Adds Five Flaws to KEV Catalog: CISA added critical vulnerabilities to its Known Exploited Vulnerabilities catalog, including Apple “DarkSword” exploits (CVE-2025-31277, CVE-2025-43510, CVE-2025-43520), a Laravel Livewire flaw (CVE-2025-54068) used by MuddyWater, and a Craft CMS bug (CVE-2025-32432). Federal agencies must patch by April 3, 2026. More info
Magento “PolyShell” Command Execution: Researchers identified a critical flaw in Magento that enables attackers to execute arbitrary commands on e-commerce servers. This stems from improper handling of shell commands and poses a significant risk to consumer data and store integrity. More info
Langflow RCE (CVE-2026-33017): A critical vulnerability was discovered in Langflow, an open-source UI for building AI pipelines. The flaw allows for remote code execution by exploiting how the platform processes specific inputs during LLM flow construction. More info
🎯 Adversaries
FBI Links Signal Phishing to Russian Intelligence: Sophisticated phishing attacks targeting the Signal messaging app have been officially linked to Russian intelligence services. The operations use deceptive messages to trick high-profile targets into revealing credentials or installing malware. More info
“Handala” Group Linked to Iran: U.S. officials confirmed a direct link between the Handala hacking group and the Iranian government following an international operation to dismantle the group’s infrastructure. Handala is associated with high-profile disruptive attacks and data leaks. More info
“Beast” Ransomware Server Exposed: A ransomware group known as “Beast” accidentally exposed its backend server due to poor OpSec, providing researchers with insights into their target lists and a centralized dashboard used to manage infections. More info
Predator Spyware Bypasses iOS Recording Indicator: Analysis of Predator spyware reveals a method for bypassing the iOS green/orange recording dots using kernel-level exploits. This allows the spyware to record audio and video covertly without visual alerts. More info
Four Major Botnets Disrupted: A joint international operation successfully disrupted the Aisuru, Kimwolf, Jackskid, and Mossad botnets. These networks were primarily used for large-scale DDoS attacks and ransomware distribution. More info
📈 Trends
VoidStealer Targets Chrome via Debugger Trick: A new malware variant, VoidStealer, attaches a debugger to the Chrome process to exfiltrate the browser’s master key. This allows attackers to decrypt saved passwords, cookies, and autofill data by bypassing standard security protections. More info
Android “Advanced Flow” for Sideloading: Google has introduced a new security workflow for Android to mitigate risks from APK sideloading. It adds additional verification steps and warnings when users install apps from third-party sources. More info
Azure Monitor Alerts Abused in Callback Phishing: Cybercriminals are abusing Microsoft Azure Monitor alerts in callback phishing campaigns. Attackers send fraudulent notifications that prompt users to call a fake support number to “resolve” system issues. More info
Fake Zoom Invites Spread Malware: A malware campaign is utilizing fake Zoom meeting invitations to infect Windows PCs. The links download a malicious executable that installs data-stealing malware or ransomware. More info
Malicious Python Scripts in Repositories: A SANS ISC report highlights malicious Python scripts in popular package repositories designed to harvest system information. This follows a trend of “typosquatting” attacks within the Python ecosystem. More info
💥 Breaches & Leaks
Trivy Scanner Supply Chain Attack: A supply chain attack targeting the Trivy security scanner resulted in a self-triggering infostealer executing through GitHub Actions. The breach allowed attackers to harvest environment variables and credentials. More info
Proton Mail Shared Information with Police: Proton Mail shared user metadata and IP addresses with law enforcement following a legal request. The incident highlights that while content remains encrypted, metadata can be legally compelled. More info
Magento Defacement Campaign Hits Thousands: Thousands of Magento e-commerce sites have been impacted by an ongoing defacement campaign. Attackers are exploiting known vulnerabilities to inject malicious scripts and alter storefronts. More info